Domain Kiosk
Creative website design and internet marketing studio
How to stake LOCs securely and conveniently on Raspberry Pi 3B+
This article is the second in a series that helps begin staking LOCs on the Raspberry Pi 3b+.
In the previous article we discussed how to recompile the LOC staking wallet, and we showed that it is possible to recompile and also use the QT version (with the Graphical User Interface - GUI) on the Pi. Why we needed to do that? Well, staking with the GUI is much more convenient. The QT version in fact does not take up a lot of memory and the Pi can work perfectly well with it.
What do we show you in this article?
- How to set up the SSH session between your every-day computer and the Pi.
- How to set up the VNC server/client on your computer and the Pi, so that you can use the QT version of the wallet on the Pi and have the GUI remotely displayed on your PC.
- How to set up a tunnel, which will allow you to pass the VNC data though the SSH connection, and thus eliminate the need for a port specific for the VNC. The purpose is to minimize the number of the open listening ports on the Pi. After you establish the tunnel, you will have just one single port to protect (for the SSH session), instead of two (one for the SSH and a second one for the VNC connection).
- How to set up the firewall on the Pi, with all ports closed, except the one for SSH. Also when the firewall is enabled, we set a rule that will allow just one single IP address to connect to your Pi via the SSH (the IP of your every-day computer) and will disallow any other IPs.
- How to check which listening ports are still open on the firewall and set the listening port of the wallet properly through the firewall.
As a result you will be able to use remotely the GUI version of the wallet (QT) on your PI, and the only listening port to the outer world will be the necessary listening port for the LOC staking wallet to function in the blockchain. All other ports will be closed or only listening (for the SSH session) to your every-day computer (where you access the Pi from).
We recommend using the Raspbian OS for the Pi with desktop. The desktop is very helpful to quickly understand and learn the filesystem of the OS. If you haven't done already, first you should prepare the Pi as described in section "1. Prepare the Raspberry Pi" from our previous article.
1. Set up the SSH session
Here is the official guide how to set up SSH on your Pi >> Remote access with SSH.
It should be noted that you can use SSH on your LAN or on the Internet. You need fixed local IP addresses on your LAN both for the Pi and the remote machine (the computer you access the Pi from). In this case you are behind a NAT (Network address translation protocol) on your router, which brings an extra layer of protection for the Pi from outside hackers. If you want a setup to access the Pi over the Internet you will need one fixed public IP address for the Pi and another one for your remote machine.
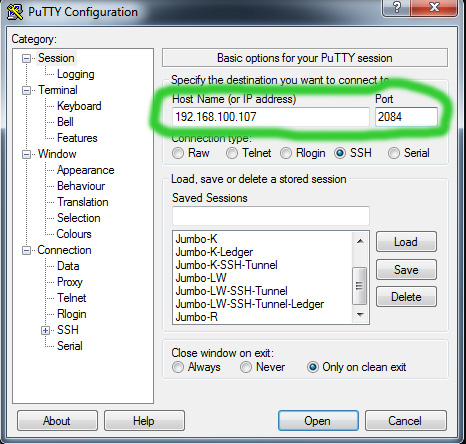
The default SSH port used on the Pi is port 22. It is highly recommended to change that port to a custom one, different from 22. To do this you open a SSH session with the Pi and edit the file "/etc/ssh/sshd_config":
sudo nano /etc/ssh/sshd_config
In this file you find the line:
# Port 22
Uncomment the line and change the default port. For example it should look like this:
Port 2084
Save the file and reboot your Pi. Now you will access remotely the Pi via SSH on port 2084.
2. Set up the VNC server/client
Here is the official guide how to set up VNC on your Pi >> Remote access with VNC.
There are many different flavors of VNC available to remotely access and manage a server with graphical interface. Raspbian Stretch with desktop comes with RealVNC ready to use. The connection is very well secured, you can use a password or a pair of keys to access the server and the connection is encrypted. And this level of security can be quite sufficient for many users. We would want however to go further and keep control of security in our own hands, and may be use a different VNC client, which we are used to and like.
The following steps are for users that would like to keep security under control and don't just blindly rely on RealVNC integrity.
First on the Pi we enable the RealVNC server. Here in this example the remote PC (where we access the Pi from) is a Windows 7 machine. We install the RealVNC client on the remote PC and establish a secure connection with the Pi.
A sample scenario (Access the Pi remotely from Windows 7 PC on LAN):
- Establish SSH session from your Windows PC with Putty:
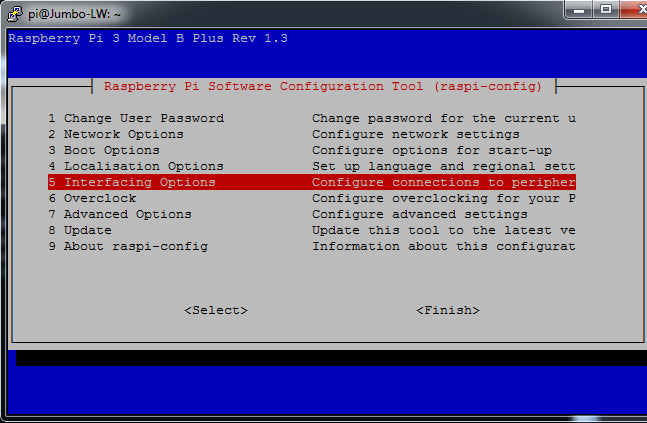
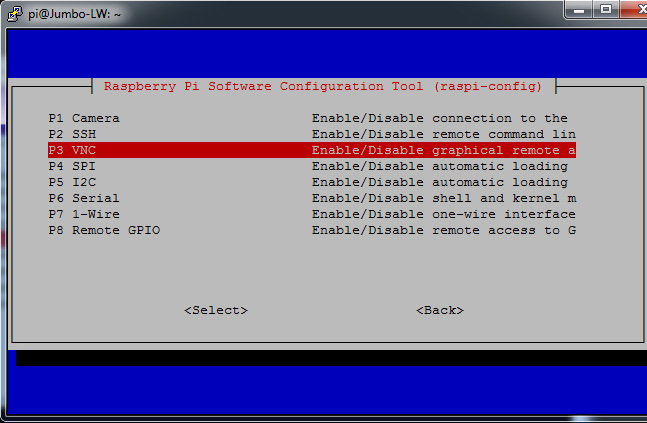
- Enable RealVNC server if not enabled already:
sudo raspi-config
Then Interfacing Options > VNC > Select and confirm "YES" and reboot.
- Install RealVNC viewer (client) on your Windows 7 PC >> RealVNC viewer download.
- Set up RealVNC viewer and make first connection with the RealVNC server on the Pi:
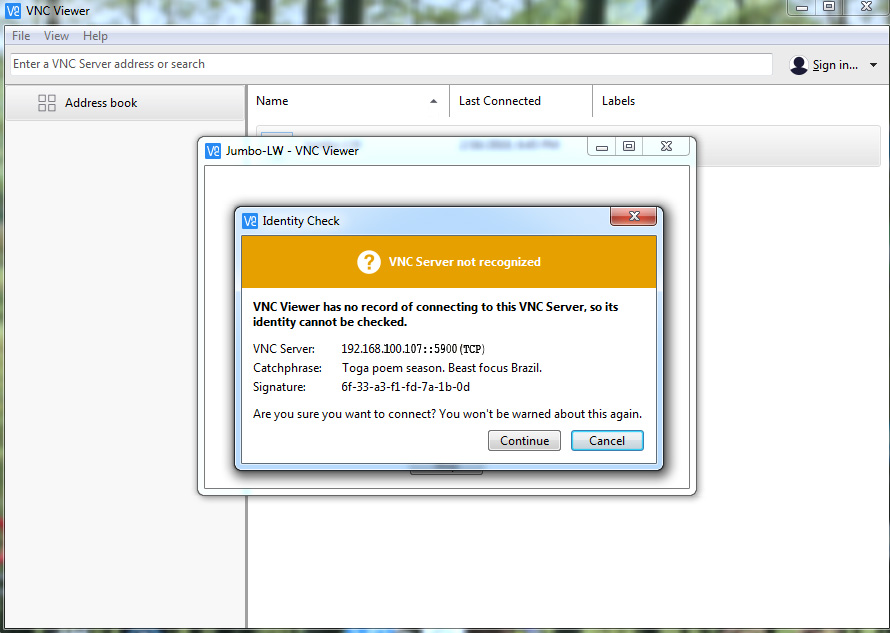
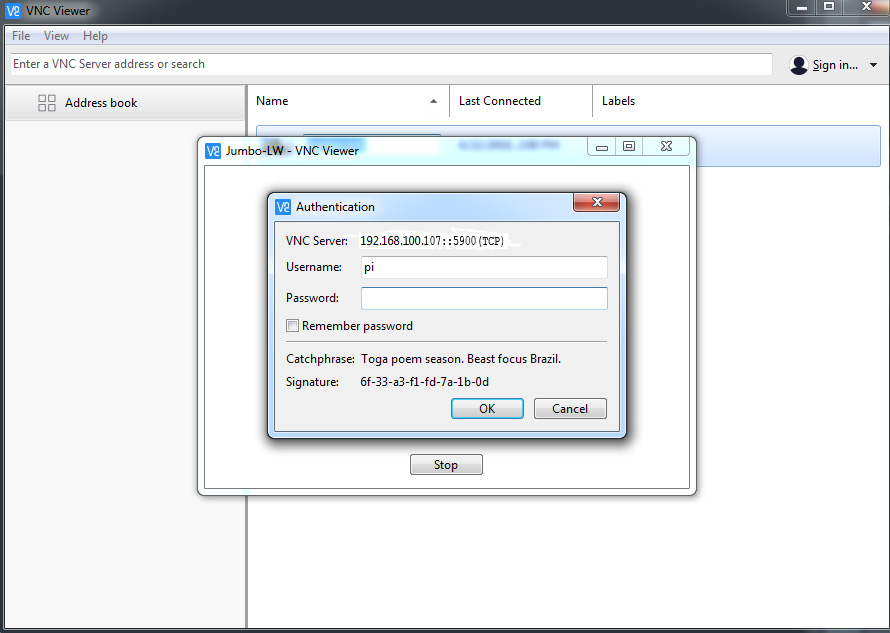
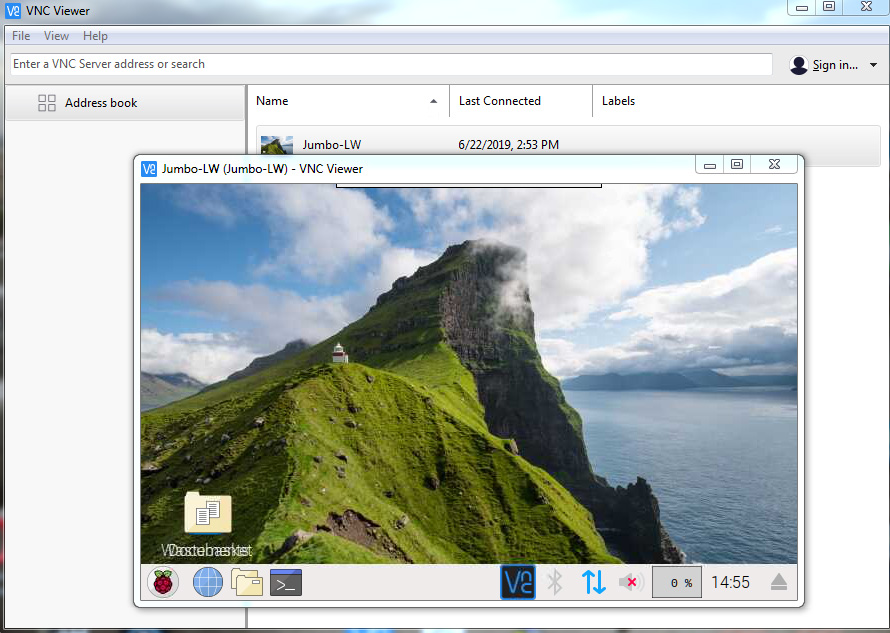
You can explore a bit the Raspbian Stretch desktop now, remotely from your Windows PC.
- Now we will disable the encryption on the RealVNC server and this will allow us to use as remote client almost any other VNC client, in other words our favorite VNC client, to access the RealVNC server on the Pi. Remember, we will pass the VNC connection via tunnel on SSH session, and SSH is already encrypted. Here is how to disable encryption on the RealVNC server:
Right-click with the mouse on your connection in the RealVNC viewer and click Properties.
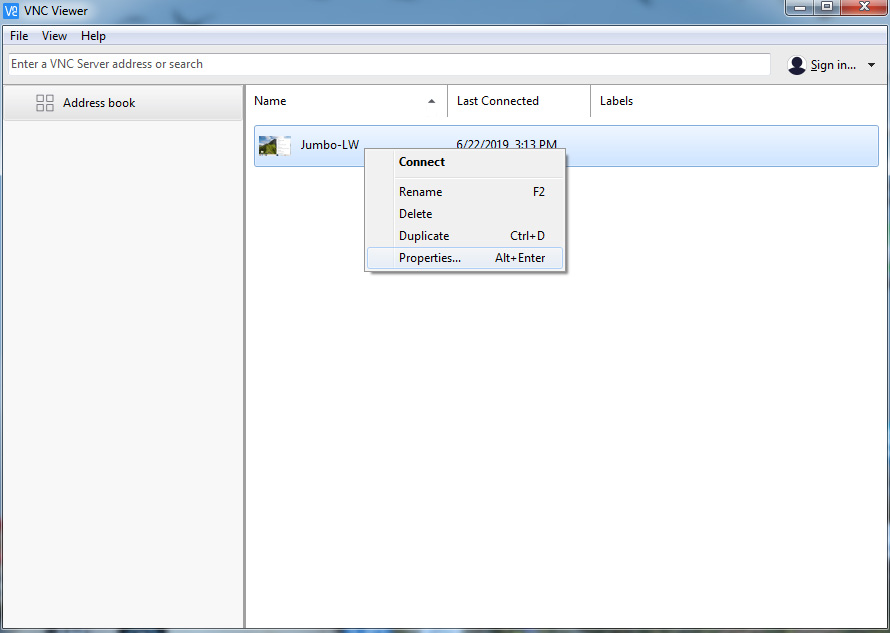
Now in the drop-down menu Encryption select the option Prefer off and click OK.
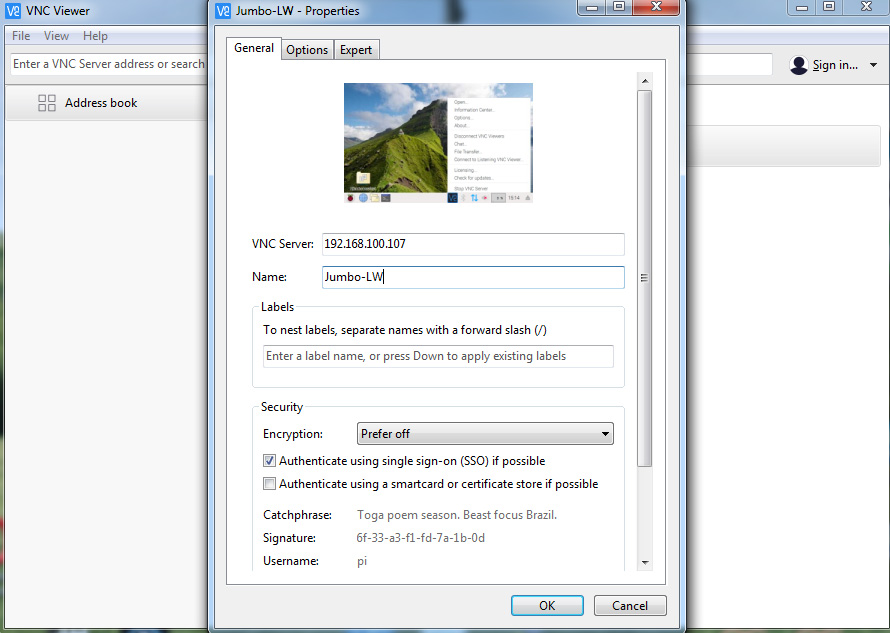
Try connecting to be sure the VNC connection works with this setting correctly.
- Start the RealVNC server via SSH with a command that will create a virtual desktop with the desired geometry (window size) and with custom listening port (5914) for the VNC server:
vncserver :14 -geometry 1250x900 -depth 24 -nolisten tcp
You can also make a short command for ease of use in the "/usr/local/bin" directory:
sudo nano /usr/local/bin/startVNC
The contents of the file should be:
#!/bin/bash
vncserver :14 -geometry 1250x900 -depth 24 -nolisten tcp
Make this file executable:
sudo chmod +x /usr/local/bin/startVNC
Now to start the RealVNC server with custom port 5914 you just type in the SSH session window:
startVNC
It is also recommended to disable the autostart of the RealVNC server on the default port 5900 every time you reboot the Pi. For this you simply disable VNC with "sudo reaspi-config". Then launch the VNC server with the short command startVNC.
- Next we install TurboVNC client on the Windows 7 machine, from here >> TurboVNC files.
After you start the RealVNC server (type startVNC in SSH session), you use the following settings in the TurboVNC viewer on your remote PC to connect:
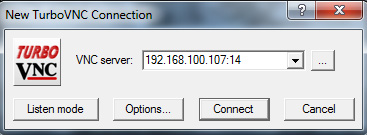
If you can access the RealVNC server on the Pi with the TurboVNC viewer (client), then you have completed successfully this step. In a similar way you can use a MAC or even another Pi with a monitor and keyboard to remotely access the RealVNC server with the LOC wallet. You are ready for the next step.
3. Set up a tunnel for VNC through the SSH connection
- This is the command that will start the VNC server with port listening to the local machine (we just added the option -localhost to the command we used before):
vncserver :14 -geometry 1250x900 -depth 24 -localhost -nolisten tcp
You can also make a short command for ease of use in the "/usr/local/bin" directory:
sudo nano /usr/local/bin/startVNC-local
The contents of the file should be:
#!/bin/bash
vncserver :14 -geometry 1250x900 -depth 24 -localhost -nolisten tcp
Make this file executable:
sudo chmod +x /usr/local/bin/startVNC-local
Now to start the RealVNC server to listen to the local machine (127.0.0.1) you just type in the SSH session window:
startVNC-local
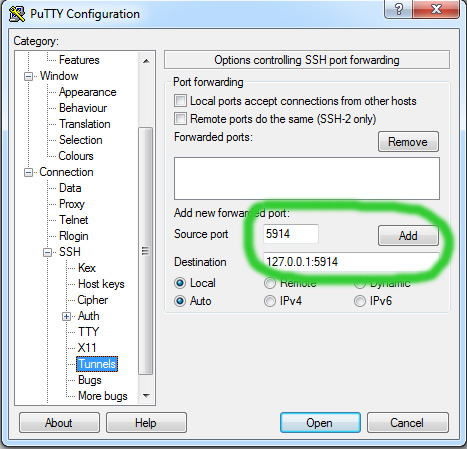
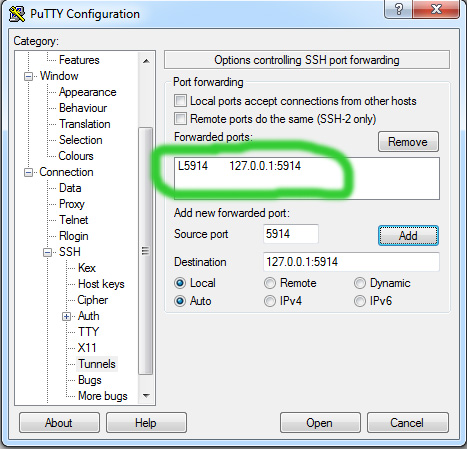
- Next you set up Putty on Windows to establish the tunnel when SSH session is started. You make the follwing settings in Putty:
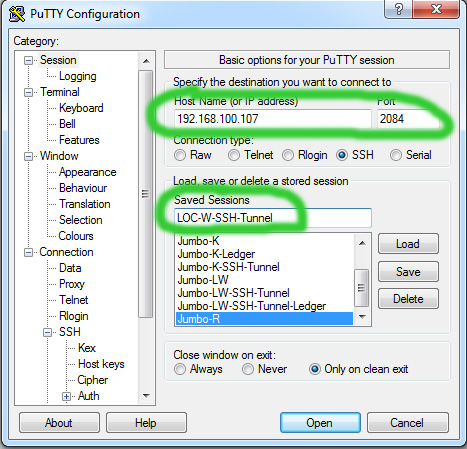
Give a name to your SSH connection and save it for easy access later:
- Finally after you start the SSH session with tunnel, you start the VNC viewer with this setting:
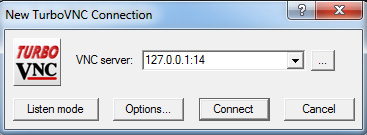
You have successfully established the VNC connection in a tunnel on SSH session.
4. Set up the firewall on the Pi
The most used and easy to use firewall is UFW (Uncomplicated FireWall). Here is one of the many guides that exist >> UFW Debian Wiki.
Here is how we setup on the Pi with the LOC staking wallet:
- Before you enable the UFW you should set a rule that will exclude you local IP address from being blocked by the firewall. Otherwise, in case you access the Pi remotely, you will get blocked out by the firewall. Here is the rule to set up:
sudo ufw allow from 192.168.100.103
where 192.168.100.103 is your local IP address on your Windows (remote) machine.
- Set a rule to allow the listening port of the LOC staking wallet:
sudo ufw allow 1337/tcp
- Check the status:
sudo ufw status verbose
- Delete a rule:
sudo ufw delete x (where x is the consequential number of the rule to be deleted)
- Disable the firewall:
sudo ufw disable
- Enable the firewall:
sudo ufw enable
Here is what you should have after all rules are in place and the ufw is enabled. Pay attention all incoming ports are closed by default:
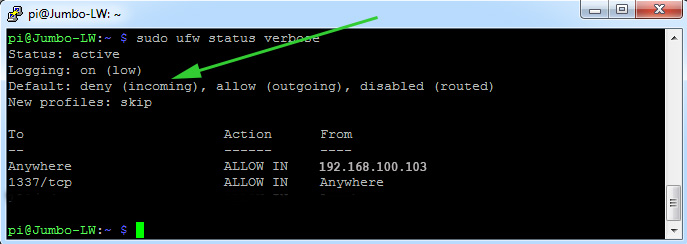
Now we've arrived at the last, but also very important step - checking if all ports are set up correctly.
5. Check listening ports
- Check listening ports with netstat command:
sudo netstat -nlpt
You should see the following result:
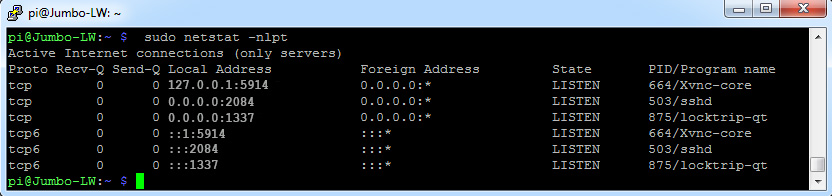
The first open port is 5914 and this is VNC server listening to the local machine for a tunnel. The second open port is 2084 and this is the SSH server listening to the internet for connections. The last open port is 1337 and this is the staking wallet listening for connections. The last three rows show the same ports on IPv6, but they are not listening to anywhere, because we have disabled IPv6.
- Useful third party services to check your open ports:
1. A free program that you can download and check open ports on a specific device in your LAN >> Advanced Port Scanner.
2. A free online service to check single open ports how they are seen from the internet >> YouGetSignal.
The above steps should have helped you to professionally secure the LOC staking wallet on the Pi. This setup can be used even when your Pi is far away from you and you can access it securely on the Internet (from work for example), without fear of third party eavesdropping on your connection. Only one important piece of the puzzle is missing, which is how to better protect your access to the SSH session. This we will discuss in the next article.
Related articles
The Guide to staking HYDRA on Raspberry Pi 4b
The Guide to staking LOCs on Raspberry Pi 4b (Pre-Hydra Testnet)
- Raspberry Pi 4b - basic setup with Raspbian Buster and getting ready to install the LOC staking wallet
- Recompiling and installing of LOC staking wallet with GUI on Raspberry Pi 4b
- Basic security check list for staking LOCs on Raspberry Pi 4 model b
- Using Ledger Nano S to protect the SSH session to the Raspberry Pi 4b with LOC staking wallet
The Guide to staking LOCs on Raspberry Pi 3b+ (Pre-Hydra Testnet)
Yours, Crypto Qu
Ways to support my work, if you find it helpful. Thank You!
Book with LockTrip
 Save up to 60% on hotel reservations with Locktrip booking engine!
Save up to 60% on hotel reservations with Locktrip booking engine!
Extra 5% discount for first booking with code Y8XVQ
Go to Locktrip ...
Our clients' websites 'live':
www.cellular-concrete.net www.ionitech.com www.nikol-n.bg www.stroitel-bg.com
Newest projects: www.hydragon.blog
 Scan QR code for LOC wallet address to send donation to
Scan QR code for LOC wallet address to send donation to Comments are helping improve the article quality and are of great value for me!
Comments are helping improve the article quality and are of great value for me! Scan QR code for HYDRA wallet address to send donation to
Scan QR code for HYDRA wallet address to send donation to Home of Digital Assets. Since 2014.
Home of Digital Assets. Since 2014. Scan QR code for BTC wallet address to send donation to
Scan QR code for BTC wallet address to send donation to